Bitcoin and hackers!
Don’t tell me you’ve never watched a TV series, where Special Agents identify the thief thanks to their new top algorithm just written 5 minutes ago by the geek?
I confess I did, and have to admit, it looks like a joke. But I recon there is some truth to it… So today we are going to explain how to identify a cryptohacker network.
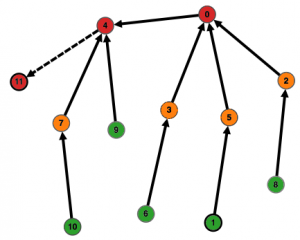
Here is what a cryptohackers’ network looks like:
What is a cryptohacker ? Why use Bitcoins?
A cryptohacker is a criminal, robbing people after putting a virus on a victim’s personal (or a company) computer and blocks this computer by encrypting all the files.
The files become an hostage and a ransom is required to free the victim’s computer. The ransom is usually paid in bitcoins, due to the idea that Bitcoin is a totally anonymous platform.
Finding hackers is a data analytics subject we are working on. Bitcoin platforms have to deal with these kind of issues and we provide them Big Data expertise. These matters can be summed up as a transactional graph analytics issue. Since each node usually has around 500 transaction links to other nodes, we count in dozen millions nodes and very large data volumes. And the Ezako team loves Big Data!
Starting the criminal investigation:
The victim sometimes goes to the Police (before or after the ransom is paid) and Police Officers investigate the Bitcoin exchange platform that sent and received the money. These platforms easily cooperate since they have a huge incentive to make their business trusted: They are the bankers of the future and are willing to gain customer trust.
How to catch a cryptohacker?
The Bitcoin platform has access to all transactions, including the fraudulent transaction.
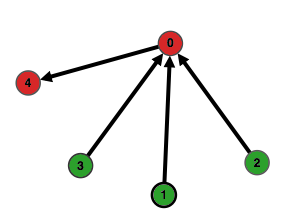
There is a simple example:
In this case, customer 1 declares account 0 as a hacker he had to pay a ransom to. This transaction from 1 to 0 has the victim as input and the hacker as output. Analysing transactions from node 0, allows us to notice that 2 and 3 are also potential victims and 4 is probably also a hacker’s account. The hacker transfers the money from 0 to 4 to eliminate his footsteps.
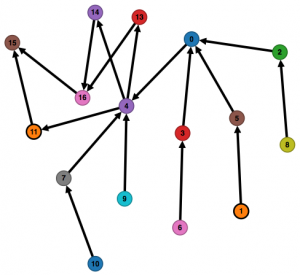
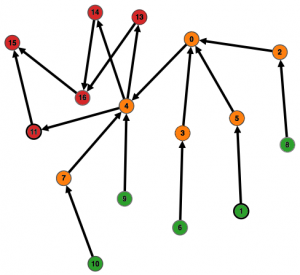
But the reality is much more complex, since each hacker uses many Bitcoin addresses (equivalent to bank accounts) to be anonymous:
In this more evolved example, 1 is identified as a victim. It is already, much more complex to identify other potential victims and hackers. Nevertheless, we notice that all the money seems to converge to address 11. This is therefore probably a hub account to concentrate the ransom from a (group of) hacker.
I hope everything is clear and easy up to here? OK, then let’s move on to the real issue: To eliminate their footsteps, hackers mix their revenues using transactions with several input accounts and several output accounts (yes, you can do that with bitcoins), and this gets the fraudulent revenues diluted. This is a way to clean dirty money.
The main difference with the previous case is mostly on address 4, which seems to be the main hub of the money laundry machine, redistributing money to several nodes. It becomes really hard to tell the difference between a regular legal online shop and a hacker.
A first simple solution to identify main hackers’ accounts would be to count incoming transactions from victims to every account:
| Address | incoming transactions count |
| 1 | 0 |
| 2 | 1 |
| 3 | 1 |
| 4 | 10 |
| 5 | 1 |
| … | |
| 11 | 11 |
| … | |
| 15 | 17 |
We can then easily see which account should be under surveillance as a potential hacker or hacking hub. This first analysis provides an easy manner to identify potentially fraudulent accounts, concentrating money from numerous transactions from hackers. Therefore it simplifies the problem. With additional analysis work, we can identify an entire network of hackers accounts.
Now you can keep thinking about methods to identify criminals, like in TV series! And next time, we’ll explain money laundering strategies for Bitcoin and new ways to identify hackers!